有时候,我很佩服我自己
一个非技术专业的人,从对互联网的兴趣到今天,几乎所有的东西都是自己自学来的,希望和大家共勉,但我也欠大家不要死磕,我就是一个苦逼!
起因:
一个群友加群后要搭L2TP服务,直接就加我好友,请我宵夜,我这也不好拒绝,就硬着头皮给搭建。我想的倒是简单,拿了别人的一键脚本上去就干,干完发现连不上。这下好了,折腾一下,2个小时过去了,后面还是给我把问题搞定了。下面跟大家详细介绍:
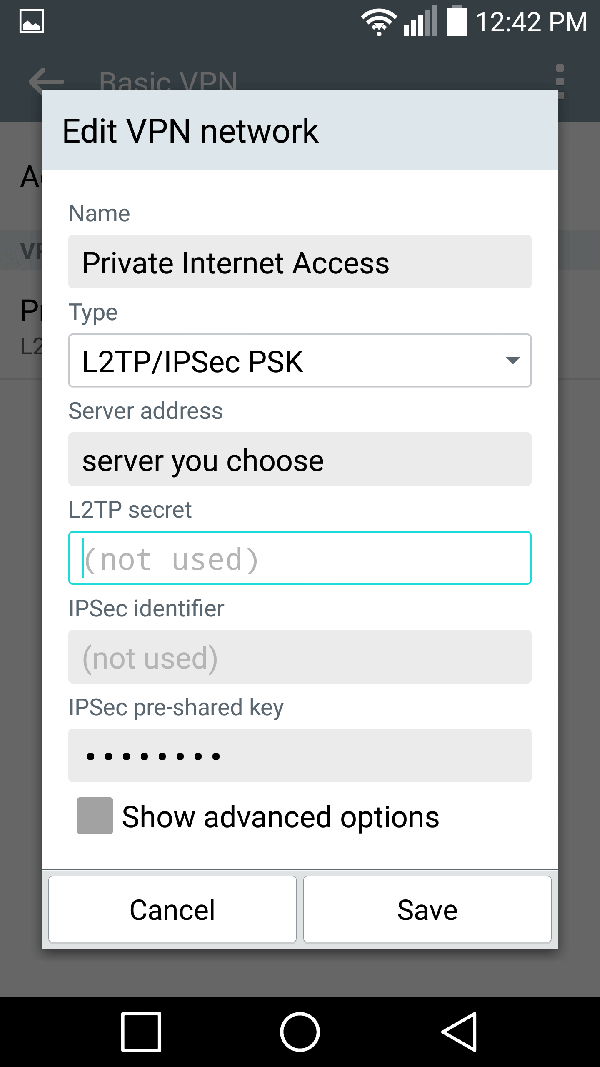
关于L2TP/IPsec:
L2TP(Layer 2 Tunneling Protocol,二层隧道协议)是VPDN(Virtual Private Dial-up Network,虚拟私有拨号网)隧道协议的一种。简单说理解为一种拨号上网的方式!
IPsec VPN 可以加密你的网络流量,以防止在通过因特网传送时,你和 VPN 服务器之间的任何人对你的数据的未经授权的访问。在使用不安全的网络时,这是特别有用的,例如在咖啡厅,机场或旅馆房间。
L2TP/IPsec的优点和缺点
优点:无需下载客户端、win10, IOS,安卓手机都用相应的链接方式。
缺点:速度和被墙概率尚未知晓。
VPS服务器选择:
安装之前,大家得保证有一台服务器,服务器可以选购:搬瓦工、Vultr、糖果主机、DigitalOcean、Hawk Host、Hostgator(国际版)、阿里云国际、腾讯云国际
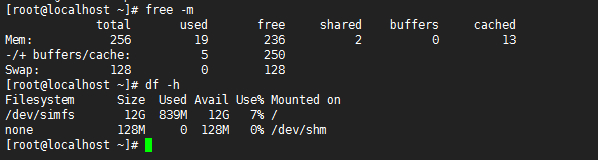
系统要求:可用于 Ubuntu/Debian/CentOS 系统。
Ubuntu LTS, Debian一键脚本:
wget https://git.io/vpnsetup -O vpnsetup.sh && sudo sh vpnsetup.sh下面为Centos 6 / 7 或者其他更高版本安装方法
Centos 搭建方法步骤如下:(需要帮忙搭建请加群联系群主)
[一]: 新建一个文件 install_wervpsl2tp
连接ssh后,执行命令vi install_wervpsl2tp, 然后按键i进入编辑模式,然后鼠标点击右键,选择粘贴, 将下面这部分代码粘贴进去.
粘贴完成后, 按Esc键,然后依次按键盘:wq(冒号,w,q),然后,按回车键
文件内容如下:
#!/bin/sh # # Script for automatic setup of an IPsec VPN server on CentOS/RHEL 6 and 7. # Works on any dedicated server or virtual private server (VPS) except OpenVZ. # # DO NOT RUN THIS SCRIPT ON YOUR PC OR MAC! # # The latest version of this script is available at: # https://github.com/hwdsl2/setup-ipsec-vpn # # Copyright (C) 2015-2019 Lin Song <[email protected]> # Based on the work of Thomas Sarlandie (Copyright 2012) # # This work is licensed under the Creative Commons Attribution-ShareAlike 3.0 # Unported License: http://creativecommons.org/licenses/by-sa/3.0/ # # Attribution required: please include my name in any derivative and let me # know how you have improved it! # ===================================================== # Define your own values for these variables # - IPsec pre-shared key, VPN username and password # - All values MUST be placed inside 'single quotes' # - DO NOT use these special characters within values: \ " ' YOUR_IPSEC_PSK='' YOUR_USERNAME='' YOUR_PASSWORD='' # Important notes: https://git.io/vpnnotes # Setup VPN clients: https://git.io/vpnclients # ===================================================== export PATH="/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin" SYS_DT=$(date +%F-%T) exiterr() { echo "Error: $1" >&2; exit 1; } exiterr2() { exiterr "'yum install' failed."; } conf_bk() { /bin/cp -f "$1" "$1.old-$SYS_DT" 2>/dev/null; } bigecho() { echo; echo "## $1"; echo; } check_ip() { IP_REGEX='^(([0-9]|[1-9][0-9]|1[0-9]{2}|2[0-4][0-9]|25[0-5])\.){3}([0-9]|[1-9][0-9]|1[0-9]{2}|2[0-4][0-9]|25[0-5])$' printf '%s' "$1" | tr -d '\n' | grep -Eq "$IP_REGEX" } vpnsetup() { if ! grep -qs -e "release 6" -e "release 7" /etc/redhat-release; then exiterr "This script only supports CentOS/RHEL 6 and 7." fi if [ -f /proc/user_beancounters ]; then exiterr "OpenVZ VPS is not supported. Try OpenVPN: github.com/Nyr/openvpn-install" fi if [ "$(id -u)" != 0 ]; then exiterr "Script must be run as root. Try 'sudo sh $0'" fi def_iface=$(route 2>/dev/null | grep -m 1 '^default' | grep -o '[^ ]*$') [ -z "$def_iface" ] && def_iface=$(ip -4 route list 0/0 2>/dev/null | grep -m 1 -Po '(?<=dev )(\S+)') def_state=$(cat "/sys/class/net/$def_iface/operstate" 2>/dev/null) if [ -n "$def_state" ] && [ "$def_state" != "down" ]; then case "$def_iface" in wl*) exiterr "Wireless interface '$def_iface' detected. DO NOT run this script on your PC or Mac!" ;; esac NET_IFACE="$def_iface" else eth0_state=$(cat "/sys/class/net/eth0/operstate" 2>/dev/null) if [ -z "$eth0_state" ] || [ "$eth0_state" = "down" ]; then exiterr "Could not detect the default network interface." fi NET_IFACE=eth0 fi [ -n "$YOUR_IPSEC_PSK" ] && VPN_IPSEC_PSK="$YOUR_IPSEC_PSK" [ -n "$YOUR_USERNAME" ] && VPN_USER="$YOUR_USERNAME" [ -n "$YOUR_PASSWORD" ] && VPN_PASSWORD="$YOUR_PASSWORD" if [ -z "$VPN_IPSEC_PSK" ] && [ -z "$VPN_USER" ] && [ -z "$VPN_PASSWORD" ]; then bigecho "VPN credentials not set by user. Generating random PSK and password..." VPN_IPSEC_PSK=$(LC_CTYPE=C tr -dc 'A-HJ-NPR-Za-km-z2-9' < /dev/urandom | head -c 20) VPN_USER=vpnuser VPN_PASSWORD=$(LC_CTYPE=C tr -dc 'A-HJ-NPR-Za-km-z2-9' < /dev/urandom | head -c 16) fi if [ -z "$VPN_IPSEC_PSK" ] || [ -z "$VPN_USER" ] || [ -z "$VPN_PASSWORD" ]; then exiterr "All VPN credentials must be specified. Edit the script and re-enter them." fi if printf '%s' "$VPN_IPSEC_PSK $VPN_USER $VPN_PASSWORD" | LC_ALL=C grep -q '[^ -~]\+'; then exiterr "VPN credentials must not contain non-ASCII characters." fi case "$VPN_IPSEC_PSK $VPN_USER $VPN_PASSWORD" in *[\\\"\']*) exiterr "VPN credentials must not contain these special characters: \\ \" '" ;; esac bigecho "VPN setup in progress... Please be patient." # Create and change to working dir mkdir -p /opt/src cd /opt/src || exit 1 bigecho "Installing packages required for setup..." yum -y install wget bind-utils openssl \ iptables iproute gawk grep sed net-tools || exiterr2 bigecho "Trying to auto discover IP of this server..." cat <<'EOF' In case the script hangs here for more than a few minutes, press Ctrl-C to abort. Then edit it and manually enter IP. EOF # In case auto IP discovery fails, enter server's public IP here. PUBLIC_IP=${VPN_PUBLIC_IP:-''} [ -z "$PUBLIC_IP" ] && PUBLIC_IP=$(dig @resolver1.opendns.com -t A -4 myip.opendns.com +short) check_ip "$PUBLIC_IP" || PUBLIC_IP=$(wget -t 3 -T 15 -qO- http://ipv4.icanhazip.com) check_ip "$PUBLIC_IP" || exiterr "Cannot detect this server's public IP. Edit the script and manually enter it." bigecho "Adding the EPEL repository..." epel_url="https://dl.fedoraproject.org/pub/epel/epel-release-latest-$(rpm -E '%{rhel}').noarch.rpm" yum -y install epel-release || yum -y install "$epel_url" || exiterr2 bigecho "Installing packages required for the VPN..." REPO1='--enablerepo=epel' REPO2='--enablerepo=*server-optional*' REPO3='--enablerepo=*releases-optional*' yum -y install nss-devel nspr-devel pkgconfig pam-devel \ libcap-ng-devel libselinux-devel curl-devel \ flex bison gcc make ppp || exiterr2 yum "$REPO1" -y install xl2tpd || exiterr2 if grep -qs "release 6" /etc/redhat-release; then yum -y remove libevent-devel yum "$REPO2" "$REPO3" -y install libevent2-devel fipscheck-devel || exiterr2 else yum -y install systemd-devel iptables-services || exiterr2 yum "$REPO2" "$REPO3" -y install libevent-devel fipscheck-devel || exiterr2 fi case "$(uname -r)" in 4.1[456]*) if grep -qs "release 6" /etc/redhat-release; then L2TP_VER=1.3.12 l2tp_dir="xl2tpd-$L2TP_VER" l2tp_file="$l2tp_dir.tar.gz" l2tp_url="https://github.com/xelerance/xl2tpd/archive/v$L2TP_VER.tar.gz" yum "$REPO2" "$REPO3" -y install libpcap-devel || exiterr2 wget -t 3 -T 30 -nv -O "$l2tp_file" "$l2tp_url" || exit 1 /bin/rm -rf "/opt/src/$l2tp_dir" tar xzf "$l2tp_file" && /bin/rm -f "$l2tp_file" cd "$l2tp_dir" && make -s 2>/dev/null && PREFIX=/usr make -s install cd /opt/src || exit 1 /bin/rm -rf "/opt/src/$l2tp_dir" fi ;; esac bigecho "Installing Fail2Ban to protect SSH..." yum "$REPO1" -y install fail2ban || exiterr2 bigecho "Compiling and installing Libreswan..." SWAN_VER=3.27 swan_file="libreswan-$SWAN_VER.tar.gz" swan_url1="https://github.com/libreswan/libreswan/archive/v$SWAN_VER.tar.gz" swan_url2="https://download.libreswan.org/$swan_file" if ! { wget -t 3 -T 30 -nv -O "$swan_file" "$swan_url1" || wget -t 3 -T 30 -nv -O "$swan_file" "$swan_url2"; }; then exit 1 fi /bin/rm -rf "/opt/src/libreswan-$SWAN_VER" tar xzf "$swan_file" && /bin/rm -f "$swan_file" cd "libreswan-$SWAN_VER" || exit 1 cat > Makefile.inc.local <<'EOF' WERROR_CFLAGS = USE_DNSSEC = false USE_DH31 = false USE_GLIBC_KERN_FLIP_HEADERS = true EOF NPROCS=$(grep -c ^processor /proc/cpuinfo) [ -z "$NPROCS" ] && NPROCS=1 make "-j$((NPROCS+1))" -s base && make -s install-base cd /opt/src || exit 1 /bin/rm -rf "/opt/src/libreswan-$SWAN_VER" if ! /usr/local/sbin/ipsec --version 2>/dev/null | grep -qF "$SWAN_VER"; then exiterr "Libreswan $SWAN_VER failed to build." fi bigecho "Creating VPN configuration..." L2TP_NET=${VPN_L2TP_NET:-'192.168.42.0/24'} L2TP_LOCAL=${VPN_L2TP_LOCAL:-'192.168.42.1'} L2TP_POOL=${VPN_L2TP_POOL:-'192.168.42.10-192.168.42.250'} XAUTH_NET=${VPN_XAUTH_NET:-'192.168.43.0/24'} XAUTH_POOL=${VPN_XAUTH_POOL:-'192.168.43.10-192.168.43.250'} DNS_SRV1=${VPN_DNS_SRV1:-'8.8.8.8'} DNS_SRV2=${VPN_DNS_SRV2:-'8.8.4.4'} DNS_SRVS="\"$DNS_SRV1 $DNS_SRV2\"" [ -n "$VPN_DNS_SRV1" ] && [ -z "$VPN_DNS_SRV2" ] && DNS_SRVS="$DNS_SRV1" # Create IPsec config conf_bk "/etc/ipsec.conf" cat > /etc/ipsec.conf <<EOF version 2.0 config setup virtual-private=%v4:10.0.0.0/8,%v4:192.168.0.0/16,%v4:172.16.0.0/12,%v4:!$L2TP_NET,%v4:!$XAUTH_NET protostack=netkey interfaces=%defaultroute uniqueids=no conn shared left=%defaultroute leftid=$PUBLIC_IP right=%any encapsulation=yes authby=secret pfs=no rekey=no keyingtries=5 dpddelay=30 dpdtimeout=120 dpdaction=clear ike=aes256-sha2,aes128-sha2,aes256-sha1,aes128-sha1,aes256-sha2;modp1024,aes128-sha1;modp1024 phase2alg=aes_gcm-null,aes128-sha1,aes256-sha1,aes256-sha2_512,aes128-sha2,aes256-sha2 sha2-truncbug=yes conn l2tp-psk auto=add leftprotoport=17/1701 rightprotoport=17/%any type=transport phase2=esp also=shared conn xauth-psk auto=add leftsubnet=0.0.0.0/0 rightaddresspool=$XAUTH_POOL modecfgdns=$DNS_SRVS leftxauthserver=yes rightxauthclient=yes leftmodecfgserver=yes rightmodecfgclient=yes modecfgpull=yes xauthby=file ike-frag=yes ikev2=never cisco-unity=yes also=shared EOF # Specify IPsec PSK conf_bk "/etc/ipsec.secrets" cat > /etc/ipsec.secrets <<EOF %any %any : PSK "$VPN_IPSEC_PSK" EOF # Create xl2tpd config conf_bk "/etc/xl2tpd/xl2tpd.conf" cat > /etc/xl2tpd/xl2tpd.conf <<EOF [global] port = 1701 [lns default] ip range = $L2TP_POOL local ip = $L2TP_LOCAL require chap = yes refuse pap = yes require authentication = yes name = l2tpd pppoptfile = /etc/ppp/options.xl2tpd length bit = yes EOF # Set xl2tpd options conf_bk "/etc/ppp/options.xl2tpd" cat > /etc/ppp/options.xl2tpd <<EOF +mschap-v2 ipcp-accept-local ipcp-accept-remote noccp auth mtu 1280 mru 1280 proxyarp lcp-echo-failure 4 lcp-echo-interval 30 connect-delay 5000 ms-dns $DNS_SRV1 EOF if [ -z "$VPN_DNS_SRV1" ] || [ -n "$VPN_DNS_SRV2" ]; then cat >> /etc/ppp/options.xl2tpd <<EOF ms-dns $DNS_SRV2 EOF fi # Create VPN credentials conf_bk "/etc/ppp/chap-secrets" cat > /etc/ppp/chap-secrets <<EOF "$VPN_USER" l2tpd "$VPN_PASSWORD" * EOF conf_bk "/etc/ipsec.d/passwd" VPN_PASSWORD_ENC=$(openssl passwd -1 "$VPN_PASSWORD") cat > /etc/ipsec.d/passwd <<EOF $VPN_USER:$VPN_PASSWORD_ENC:xauth-psk EOF bigecho "Updating sysctl settings..." if ! grep -qs "hwdsl2 VPN script" /etc/sysctl.conf; then conf_bk "/etc/sysctl.conf" if [ "$(getconf LONG_BIT)" = "64" ]; then SHM_MAX=68719476736 SHM_ALL=4294967296 else SHM_MAX=4294967295 SHM_ALL=268435456 fi cat >> /etc/sysctl.conf <<EOF # Added by hwdsl2 VPN script kernel.msgmnb = 65536 kernel.msgmax = 65536 kernel.shmmax = $SHM_MAX kernel.shmall = $SHM_ALL net.ipv4.ip_forward = 1 net.ipv4.conf.all.accept_source_route = 0 net.ipv4.conf.all.accept_redirects = 0 net.ipv4.conf.all.send_redirects = 0 net.ipv4.conf.all.rp_filter = 0 net.ipv4.conf.default.accept_source_route = 0 net.ipv4.conf.default.accept_redirects = 0 net.ipv4.conf.default.send_redirects = 0 net.ipv4.conf.default.rp_filter = 0 net.ipv4.conf.$NET_IFACE.send_redirects = 0 net.ipv4.conf.$NET_IFACE.rp_filter = 0 net.core.wmem_max = 12582912 net.core.rmem_max = 12582912 net.ipv4.tcp_rmem = 10240 87380 12582912 net.ipv4.tcp_wmem = 10240 87380 12582912 EOF fi bigecho "Updating IPTables rules..." # Check if rules need updating ipt_flag=0 IPT_FILE="/etc/sysconfig/iptables" if ! grep -qs "hwdsl2 VPN script" "$IPT_FILE" \ || ! iptables -t nat -C POSTROUTING -s "$L2TP_NET" -o "$NET_IFACE" -j MASQUERADE 2>/dev/null \ || ! iptables -t nat -C POSTROUTING -s "$XAUTH_NET" -o "$NET_IFACE" -m policy --dir out --pol none -j MASQUERADE 2>/dev/null; then ipt_flag=1 fi # Add IPTables rules for VPN if [ "$ipt_flag" = "1" ]; then service fail2ban stop >/dev/null 2>&1 iptables-save > "$IPT_FILE.old-$SYS_DT" iptables -I INPUT 1 -p udp --dport 1701 -m policy --dir in --pol none -j DROP iptables -I INPUT 2 -m conntrack --ctstate INVALID -j DROP iptables -I INPUT 3 -m conntrack --ctstate RELATED,ESTABLISHED -j ACCEPT iptables -I INPUT 4 -p udp -m multiport --dports 500,4500 -j ACCEPT iptables -I INPUT 5 -p udp --dport 1701 -m policy --dir in --pol ipsec -j ACCEPT iptables -I INPUT 6 -p udp --dport 1701 -j DROP iptables -I FORWARD 1 -m conntrack --ctstate INVALID -j DROP iptables -I FORWARD 2 -i "$NET_IFACE" -o ppp+ -m conntrack --ctstate RELATED,ESTABLISHED -j ACCEPT iptables -I FORWARD 3 -i ppp+ -o "$NET_IFACE" -j ACCEPT iptables -I FORWARD 4 -i ppp+ -o ppp+ -s "$L2TP_NET" -d "$L2TP_NET" -j ACCEPT iptables -I FORWARD 5 -i "$NET_IFACE" -d "$XAUTH_NET" -m conntrack --ctstate RELATED,ESTABLISHED -j ACCEPT iptables -I FORWARD 6 -s "$XAUTH_NET" -o "$NET_IFACE" -j ACCEPT # Uncomment if you wish to disallow traffic between VPN clients themselves # iptables -I FORWARD 2 -i ppp+ -o ppp+ -s "$L2TP_NET" -d "$L2TP_NET" -j DROP # iptables -I FORWARD 3 -s "$XAUTH_NET" -d "$XAUTH_NET" -j DROP iptables -A FORWARD -j DROP iptables -t nat -I POSTROUTING -s "$XAUTH_NET" -o "$NET_IFACE" -m policy --dir out --pol none -j MASQUERADE iptables -t nat -I POSTROUTING -s "$L2TP_NET" -o "$NET_IFACE" -j MASQUERADE echo "# Modified by hwdsl2 VPN script" > "$IPT_FILE" iptables-save >> "$IPT_FILE" fi bigecho "Creating basic Fail2Ban rules..." if [ ! -f /etc/fail2ban/jail.local ] ; then cat > /etc/fail2ban/jail.local <<'EOF' [ssh-iptables] enabled = true filter = sshd action = iptables[name=SSH, port=ssh, protocol=tcp] logpath = /var/log/secure EOF fi bigecho "Enabling services on boot..." if grep -qs "release 6" /etc/redhat-release; then chkconfig iptables on chkconfig fail2ban on else systemctl --now mask firewalld 2>/dev/null systemctl enable iptables fail2ban 2>/dev/null fi if ! grep -qs "hwdsl2 VPN script" /etc/rc.local; then if [ -f /etc/rc.local ]; then conf_bk "/etc/rc.local" else echo '#!/bin/sh' > /etc/rc.local fi cat >> /etc/rc.local <<'EOF' # Added by hwdsl2 VPN script (sleep 15 modprobe -q pppol2tp service ipsec restart service xl2tpd restart echo 1 > /proc/sys/net/ipv4/ip_forward)& EOF fi bigecho "Starting services..." # Restore SELinux contexts restorecon /etc/ipsec.d/*db 2>/dev/null restorecon /usr/local/sbin -Rv 2>/dev/null restorecon /usr/local/libexec/ipsec -Rv 2>/dev/null # Reload sysctl.conf sysctl -e -q -p # Update file attributes chmod +x /etc/rc.local chmod 600 /etc/ipsec.secrets* /etc/ppp/chap-secrets* /etc/ipsec.d/passwd* # Apply new IPTables rules iptables-restore < "$IPT_FILE" # Fix xl2tpd on CentOS 7, if kernel module "l2tp_ppp" is unavailable if grep -qs "release 7" /etc/redhat-release; then if ! modprobe -q l2tp_ppp; then sed -i '/^ExecStartPre/s/^/#/' /usr/lib/systemd/system/xl2tpd.service systemctl daemon-reload fi fi # Restart services mkdir -p /run/pluto modprobe -q pppol2tp service fail2ban restart 2>/dev/null service ipsec restart 2>/dev/null service xl2tpd restart 2>/dev/null cat <<EOF ================================================ IPsec VPN server is now ready for use! Connect to your new VPN with these details: Server IP: $PUBLIC_IP IPsec PSK: $VPN_IPSEC_PSK Username: $VPN_USER Password: $VPN_PASSWORD Write these down. You'll need them to connect! Important notes: https://git.io/vpnnotes Setup VPN clients: https://git.io/vpnclients setup class:https://www.vpsdhw.com/we/2351.html ================================================ EOF } ## Defer setup until we have the complete script vpnsetup "$@" exit 0
[二]然后,修改该文件的权限
执行命令 chmod 755 install_wervpsl2tp
然后运行该脚本,执行命令./install_wervpsl2tp
执行脚本,进入安装!
[三]安装完成后会有如下提示:
IPsec VPN server is now ready for use!
Connect to your new VPN with these details:
Server IP: xx.xx.xxx.xxxx
IPsec PSK: ****************
Username: *************
Password: ***************
Write these down. You’ll need them to connect!
如果你要想对用户进行操作,可以使用如下命令:
l2tp -a 新增用户
l2tp -d 删除用户
l2tp -m 修改现有的用户的密码
l2tp -l 列出所有用户名和密码
l2tp -h 列出帮助信息
其他事项:
1、脚本在安装完成后,已自动启动进程,并加入了开机自启动。
2、脚本会改写 iptables 或 firewalld 的规则。
3、脚本安装时,会即时将安装日志写到 /root/l2tp.log 文件里,如果你安装失败,可以通过此文件来寻找错误信息。
使用命令:
ipsec status (查看 IPSec 运行状态)
ipsec verify (查看 IPSec 检查结果)
/etc/init.d/ipsec start|stop|restart|status (CentOS6 下使用)
/etc/init.d/xl2tpd start|stop|restart (CentOS6 下使用)
systemctl start|stop|restart|status ipsec (CentOS7 下使用)
systemctl start|stop|restart xl2tpd (CentOS7 下使用)
service ipsec start|stop|restart|status (Debian/Ubuntu 下使用)
service xl2tpd start|stop|restart (Debian/Ubuntu 下使用)
IPsec/L2TP VPN 客户端配置详细方法:https://github.com/hwdsl2/setup-ipsec-vpn/blob/master/docs/clients-zh.md
IPsec VPN 服务器一键安装脚本安装问题参考:https://github.com/hwdsl2/setup-ipsec-vpn/blob/master/README.md
IPsec VPN Server Docker版安装说明:https://github.com/hwdsl2/docker-ipsec-vpn-server
备用脚本:
下载
wget https://git.io/vpnsetup -O vpnsetup.sh && sudo配置脚本 nano -w vpnsetup.sh 进入编辑
开始安装 sudo sh vpnsetup.sh
备用脚本2:
wget —no–check–certificate https://raw.githubusercontent.com/teddysun/across/master/l2tp.sh
chmod +x l2tp.sh
./l2tp.sh
关于Docker的介绍以及安装使用
Docker 是一个开放源代码软件项目,让应用程序布署在软件容器下的工作可以自动化进行,借此在 Linux 操作系统上,提供一个额外的软件抽象层,以及操作系统层虚拟化的自动管理机制。
Docker 利用 Linux 核心中的资源分脱机制,例如 cgroups,以及 Linux 核心名字空间(name space),来创建独立的软件容器(containers)。这可以在单一 Linux 实体下运作,避免启动一个虚拟机造成的额外负担。
简单概括起来就是,Docker 是个容器,什么都能往里塞,你也可以理解为是一个轻量化的虚拟机。
使用 Docker 的好处就是对当前系统的环境没有破坏性,基本上一款镜像可以跑在任意包含了 Docker 的机器上,可以说是十分方便了。
本文主要介绍一下我在学习 Docker 的过程中制作的几款镜像,以及使用方法。
安装并启动 Docker
在以下操作系统里安装最新版 Docker,可以直接运行官方的安装脚本一键安装。
x86_64-centos-7 x86_64-fedora-26 x86_64-fedora-27 x86_64-fedora-28 x86_64-debian-wheezy x86_64-debian-jessie x86_64-debian-stretch x86_64-debian-buster x86_64-ubuntu-trusty x86_64-ubuntu-xenial x86_64-ubuntu-bionic x86_64-ubuntu-artful
执行脚本方法如下:
wget -qO- get.docker.com | bash
安装完成后,运行下面的命令,验证是否安装成功。
docker version
启动 Docker
systemctl start docker
查看 Docker 启动状态
systemctl status docker
允许 Docker 开机自启
systemctl enable docker
拉取镜像
docker pull hwdsl2/ipsec-vpn-server
查看搭建信息:
docker logs ipsec-vpn-server
(可选步骤)备份自动生成的 VPN 登录信息(如果有)到当前目录:
docker cp ipsec-vpn-server:/opt/src/vpn-gen.env ./
查看服务器状态
如需查看你的 IPsec VPN 服务器状态,可以在容器中运行 ipsec status 命令:
docker exec -it ipsec-vpn-server ipsec status
或者查看当前已建立的 VPN 连接:
docker exec -it ipsec-vpn-server ipsec whack --trafficstatus
更多:https://github.com/hwdsl2/docker-ipsec-vpn-server/blob/master/README-zh.md
未经允许不得转载:搬瓦工VPS_美国VPS » 教程:L2TP/IPsec VPN 服务器爬墙一键脚本安装教程 文末可打赏
 搬瓦工VPS_美国VPS
搬瓦工VPS_美国VPS